by Atousa Pilger
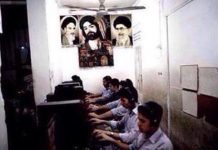
The National Council of Resistance of Iran (NCRI), considered to be the Iranian regime’s largest opposition group, recently published a report entitled, “Iran: Cyber Repression”. The NCRI’s research reveals that there are hundreds of smartphone apps that the Iranian regime is currently using to spy on its own citizens. Shockingly, many of these apps are available at Apple’s App Store, Google Play and GitHub.com, making users around the world vulnerable.
Alireza Jafarzadeh, the deputy director of the NCRI’s Washington office said, “The Iranian regime is currently hard at work to test the success of these apps on the people of Iran first.” He pointed out that the Iranian intel unit responsible for this alleged surveillance is the same group tasked with cyber warfare against the West, and added, “If not confronted, its next victims will be the people of other nations.”
Attempts to reach officials at Apple and Google failed, and the Apple Newsroom and the Google Security Blog show no recent posts regarding the allegations.
According to Apple guidelines, developers may not “include any hidden or undocumented features in your app.” Google’s policies states that, “[apps] that are deceptive, malicious, or intended to abuse or misuse any network, device, or personal data are strictly prohibited.”
GitHub has similar regulations. A representative explained the company’s policy on malware — they “do not allow anyone to use our platform for exploit delivery, such as using GitHub as a means to deliver malicious executables.” However, GitHub does not “prohibit the posting of source code which could be used to develop malware or exploits, as the publication and distribution of such source code has educational value and provides a net benefit to the security community.”
If a user believes an app to be abusive, inappropriate or otherwise in violation of company terms, GitHub, Apple and Google Play all provide portals where the app can be easily reported.
A list of the apps that are available outside of Iran, is included in the NCRI report. Despite allegations of connections to Iranian intelligence, Mobogram, Telegram Farsi, and Telegram Black are still available for download, according to an article by Alex Diaz for Fox News.
The report explains that these apps are “fork” versions of the popular messaging app, Telegram. The term “fork” is describes programs that are unofficial copies of officially-licensed programs. Many of them were designed to appeal to users looking for a messenger service that allows them to communicate in Farsi, a feature that isn’t included in Telegram. What concerns the NCRI is that they believe that these apps can record audio, and even take your picture for surveillance purposes. The NCRI says further that some of the companies behind these apps are “front companies” for the Islamic Revolutionary Guard Corps (IRGC).
During the recent turn of the year protests that broke out across Iran, estimates showed that at least 40 million people were using the official Telegram app. Fox News’ Eric Shawn was able to communicate with Iranian protesters during the unrest using a smartphone app that allowed people to speak with western media without fear of retaliation.
The Telegram app was blocked during the protests, and Iran’s apparent cyber-spying efforts quickly followed, the NCRI report suggests. They also allege that many of the people who were arrested during the protests were presented with the option “to leave the Telegram environment and enter the controlled environment of Mobogram” before being released by authorities.
Pavel Durov, founder and CEO of Telegram, suggested on Twitter last July, that “Mobogram is an outdated and potentially insecure fork of Telegram from Iran. I don’t advise to use it.”
Durov tweeted in 2015 that Iranian officials had wanted “to use @telegram to spy on their citizens.” He added, “We can not and will not help them with that.”