Tim Johnson wrote an article about the recent spate of cyberattacks. He said that two government agencies in Saudi Arabia have had an unspecified number of their computers frozen with experts saying that Iran is probably behind the chaos.
Johnson said: “The attacks are believed to have affected thousands of computers at the Saudi civil aviation and transportation agencies, harkening back to a devastating Iranian cyberattack in 2012 that nearly crippled the Saudi state oil company, Aramco.”
Saudi Arabia’s national central bank denied reports that it had been hit by a cyberattack.
Experts in the domain say that it is impossible to say for certain that the attacks that began on 17th November were carried out by hackers from Iran. However, they do note similarities with the 2012 cyberattack and confirm that Iranian hackers are particularly active.
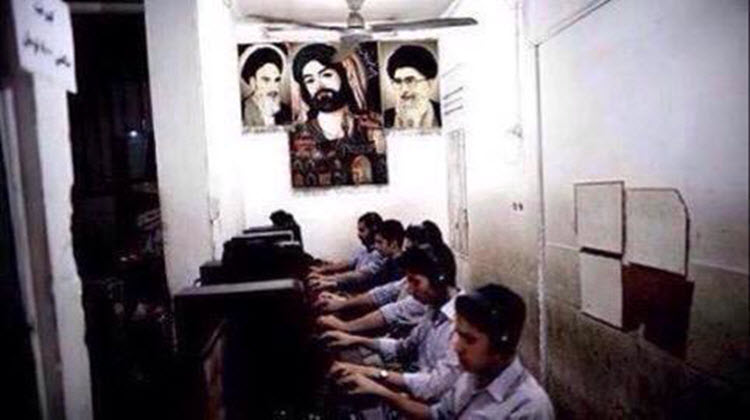
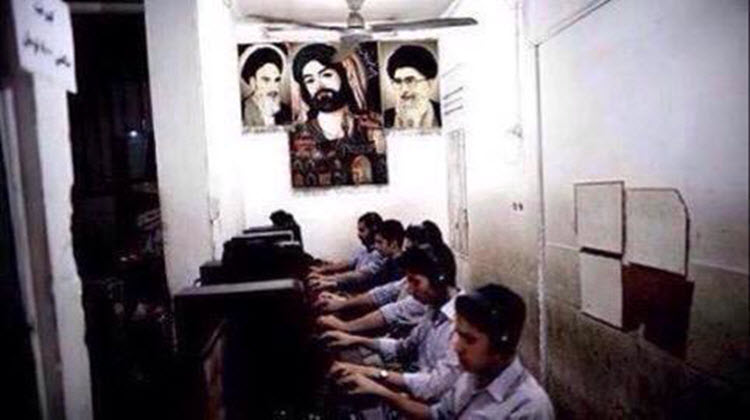
Collin Anderson, an independent researcher studying Iranian cyber warfare for the Carnegie Endowment for International Peace said: “Since the (U.S.) election especially, there’s been a pretty drastic increase in the amount of targeting of Saudi and Israeli institutions by hacking groups that we absolutely know are based out of Iran.”
He added that there is a substantial amount of evidence that ties the hacking to the Islamic Revolutionary Guard Corps (IRGC), the most powerful security and military organisation in Iran.
Johnson explained: “Cyber experts commonly refer to the malicious code infecting Saudi computers as Shamoon 2.0, a new version of the Shamoon malware that hit Aramco in 2012. The code is also known as disttrack.”
George Avetisov, cofounder and chief executive of HYPR Biometric Security, a New York City firm that deals with cybersecurity solutions, said: “The infection capability doesn’t cause any particular hardware damage we know of but it does ‘brick’ your computer.” When a computer is “bricked” it is rendered as useful as a brick, i.e. completely useless.
He said these attacks were “not particularly stealthy” and the virus spread through a specific type of software that is like a calling card from Iranian hackers.
Anderson said that Saudi Arabia has been very “opaque” about attacks like this in the past. Regarding the crime itself, he said that it was something that could be carried out with minimal risk and minimal funds.
The attack started on a Thursday evening – the start of the weekend in Saudi Arabia. Therefore, employees had left the office until Sunday leaving the virus to go unnoticed until several days later when employees returned.
Avetisov said: “Usually you see attacks of a large scale as potentially a precursor for a much larger event. It remains to be seen if that’s the case here. These are crimes of opportunity essentially. It’s really like these Iranian groups getting lucky based off of social engineering rather than, you know, highly technical operations conducted with zero day exploits.”
Johnson mentioned the U.S.-Israeli cyber worm “Stuxnet” that destroyed a great number of centrifuges that Iran was using in its nuclear weapons program.







